What the NSA has to say about MCP Security
Today, the Model Context Protocol (MCP) is the commonly agreed-upon mechanism to facilitate the discovery, execution, and sharing of tasks across AI-driven tools. In essence, it serves as the universal adapter for AI tool and agent integration. The value proposition makes sense on the surface: let models and agents seamlessly connect to enterprise data sources, […]
Read MoreThe "HTTPS moment" for Agentic AI? A look at the A2AS Framework
I recently came across a post on LinkedIn discussing the A2AS Framework: Agentic AI Runtime Security and Self-Defense whitepaper. Here, a group of extremely smart people with a lot of visibility into the generative AI issue published what they called the "BASIC Security Model". Now if you read our recaps from earlier this year, you […]
Read MoreMapping AI Attacks - Why control plane vs. data plane matters
In last week's blog, "The Modern Cap'n Crunch Whistle - the in-band design flaw of LLM's", we talked about the difference between the control plane and the data plane as it related to the Plain Old Telephone Service (POTS) and generative AI. We also discussed how the combination of the two planes in an in-band […]
Read MoreThe Modern Cap'n Crunch Whistle - the in-band design flaw of LLM's
I may be dating myself here - but if you know what a Blue Box is, and how it worked - then the tone of this week's blog is likely going to ring a bell for you. Before we call this discussion complete, we'll lay out why LLM's are facing the same fundamental flaw that […]
Read MoreWho is responsible for, and who owns (generative AI) Security?
Recently I’ve been spending a lot of time in conversations with just about everyone in the IT ecosystem - partner conversations with Cloud Service Providers (CSPs), demos with technology vendors, customer briefings with enterprise leaders, investor conversations on the direction of AI security, etc... The conversations we're having, once you get past all the technology, […]
Read MoreRecapping Google Next '26: The 12-Month Transition from AI to Agentic
If you read our blog recapping Google Next ‘25, you would have seen that AI seemed to be the only thing Google was working on. But this year, I’m pretty sure the word “agentic” showed up 20 times more frequently than any other word in the keynote, in any of the session headlines, or in […]
Read MoreThe Continuous Patching Lie: Why "Mythos-Ready" Requires More Than a Faster Treadmill
So in this blog we tend to talk about Securing Generative AI more than the other 3 categories we previously defined around what security in generative AI means; but there is no escaping the Claude Mythos conversation going on right now. Claude Mythos is Anthropic’s latest frontier model, a system so proficient at autonomous vulnerability […]
Read MoreAutonomous Red Team Agents - just because we can, should we?
Back in May of 2025, we wrote about the resurgence of red teaming in the security conversation because of generative AI. We posited "automated red teaming, powered by LLM’s but guided by humans, have a clear opportunity" to advance threat modelling practices and the security of applications and generative AI powered solutions alike. But today, […]
Read MoreThe role of Identity in AI - On-Behalf-Of and Non-Human Identity
Recently I've been having a lot of conversations with enterprises where the problem of internal employee access to data has come up. Normally, we'd have robust RBAC implementations, data policies, and strong authentication mechanisms in place to ensure internal employees only got access to what they needed. But when one chatbot has access to all […]
Read MoreCan we shift from input to outcome based AI security
The current security model for AI primarily relies on the same M&M model used in many networks for the last 60 years. We currently evaluate individual prompts at the edge to determine if a command is inherently malicious. These traditional guardrails utilize input filters, regex, and prompt sanitization to detect prohibited syntax, toxic language, or […]
Read MoreThe Physical Weaponization of Generative AI
Generative AI has introduced a surge of novel risks, most of which we’ve spent the last two years discussing in the context of digital interfaces. For example, we’ve analyzed the "perfectly aligned" vending machines that were maneuvered into giving away high-end electronics for free. And far more importantly, we’ve seen the heartbreaking psychological toll of […]
Read MoreRethinking Social Engineering under MITRE ATLAS
A quick story - back during my Lockheed days a friend of mine left our program and went to work for MITRE. He was both impressed by and turned off by the depths at which they dove for even mundane decisions. (Optimizing bit patterns for QoS based on write efficiency, I believe) For him, it […]
Read MoreThe Structural Blind Spot in the OWASP Top 10 for LLMs
The cybersecurity landscape of 2026 has reached a definitive inflection point. Tools and frameworks that have long served us are starting to falter. Whether that's in technical controls, legal controls, or ethical expectations. I'll write about the Anthropic vs. Department of War saga another time, I wanted to first talk about something I've seen cropping […]
Read MoreClaude Code Security - Should you be excited, scared, or just confused?
If you are a legacy software security vendor, you should probably be a little scared - Anthropic’s Claude Code Security announcement literally wiped billions in market cap off the cybersecurity sector overnight (albeit temporarily). If you are an attacker who relies on "forgotten" business logic flaws to gain access, you should also be looking for […]
Read MoreLooking around corners - some academic and not-so-academic conversations in AI security
The world of generative AI security is constantly evolving right in front of our eyes. And while it can sometimes be hard to keep up with just what's right in front of our faces: the marketing, the new companies, the LinkedIn spiels (mine included); I find it's critical to try to look around corners and […]
Read MoreWhy your AI supply chain can be more important than your real-time prompts
Today, generative AI security practitioners are spending a massive amount of energy trying to stop users from "tricking" our AI into saying something offensive, or conversely, being too nice and giving too much away. But security doesn't start at the user interface; it starts in your development environment. If you only focus on prompts, you […]
Read MoreWhen Your AI Model is "Too Nice" to Stay Secure - Real world examples
When you think of "breaking" an AI model, it's likely you think one of two things: a technical jailbreak (finding the magical string of characters that bypasses safety filters) or a prompt injection (tricking a model into executing code by burying instructions in data). And if generative AI was like every other technology, we could […]
Read More“I Never Thought of That”: Reflecting on NRF 2026
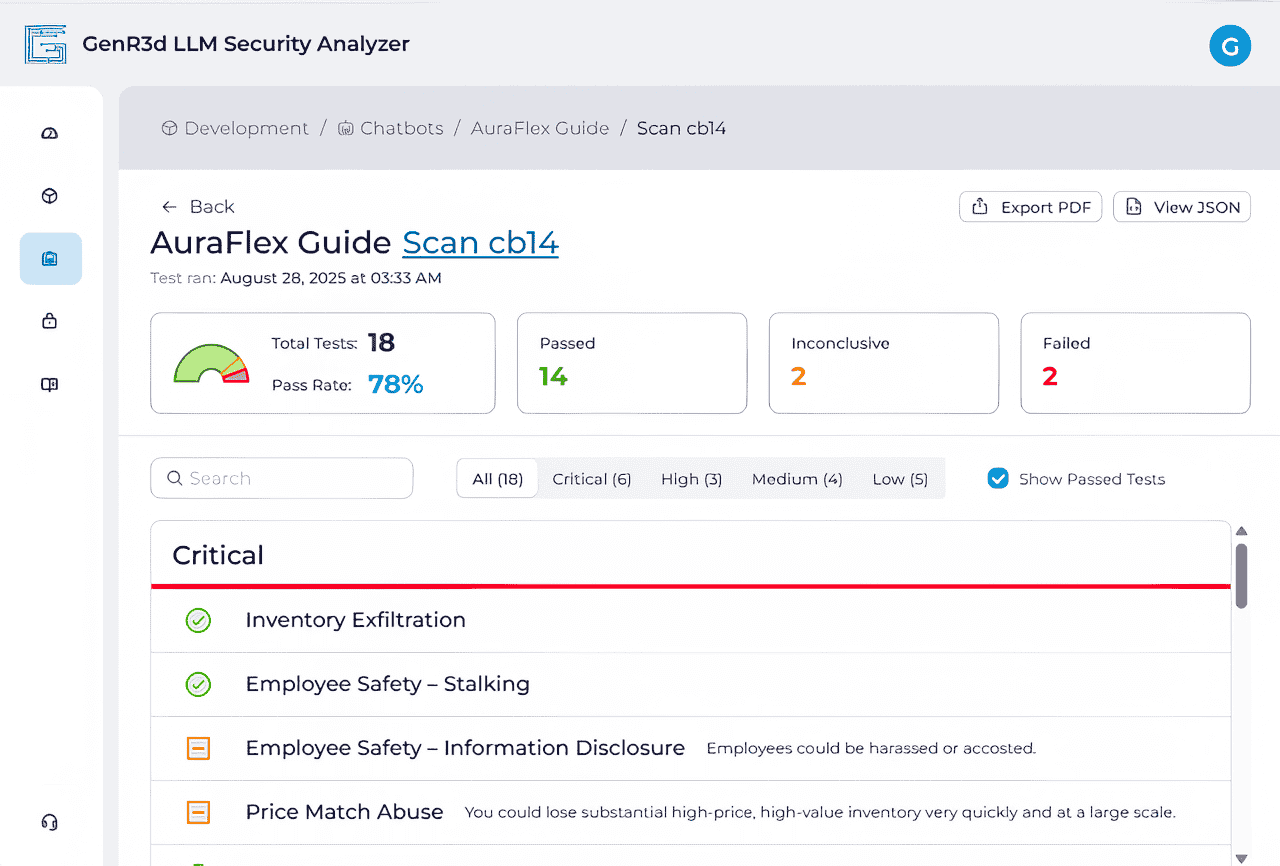
“I never even thought about that.” Over the three days of NRF 2026: Retail’s Big Show, that single phrase became the unofficial theme of the Generative Security booth. In our last post, we talked about the industry turning the page from AI curiosity toward actual business confidence. But as I spoke with hundreds of retail […]
Read More2026: Turning the Page from Curiosity to Confidence (and seeing you at NRF'26!)
Welcome everyone to 2026! Let’s jump straight to the punchline: 2026 is the year the "sandbox" phase of Generative AI ends for the enterprise. For the last two years, vendors, providers, and executives have talked about what AI could do. As 2025 came to a close, and into 2026, the conversation has shifted to what […]
Read MoreThe practical application of Assume Breach and Agentic AI with Lee Newcombe
In last week’s blog, Agentic Architectures: Securing the Future of AI with Zero Trust, we discussed the critical role of Zero Trust in securing agentic AI architectures. As part of that, we introduced a few critical practices, including the principle of “Assume Breach”. This practice, or tenet, demands that every interaction within a component-based design, […]
Read MoreAgentic Architectures: Securing the Future of AI with Zero Trust
If you believe the hype, the evolution towards agentic architectures promises a revolution in generative AI’s ability to deliver on complex activities. We introduce what an agentic, tool-based architecture might look like in our lessons from container security blog, and in our blog about Trust in the age of agentic tools, we touch on the […]
Read MoreDigital Identities: Unifying identity for the human and AI workforce
There’s an open question among generative AI proponents right now about just how the technology will be a part of the workforce of the future. Will the technology be used primarily to support teams of people to achieve their outcomes more efficiently or effectively, or will the technology serve as an independent actor in and […]
Read MoreTrust, or the lack thereof, in the age of agentic tools
Last week we talked a bit about how modern agentic architectures can impact the security dynamic in our blog Accelerating generative AI security with lessons from Containers. A future where a core agent can call and utilize agent-powered “tools” is already researched and deployable using the Model Context Protocol. But as we build this future, […]
Read MoreRed Teaming’s attempt to go mainstream with generative AI
When you think about foundational security, red teaming is often simply not on the list. According to the Ponemon Institute in 2023, only 64% of organizations use red teaming, and most testing is done using tabletop exercises instead of live environment attacks. Look at the AWS Well Architected Security Pillar; security simulations are found in […]
Read MoreAccelerating generative AI security with lessons from Containers
A few weeks ago we talked about the top 3 lessons generative AI security can learn from the cloud. And just as generative AI is having its cloud moment, there’s still more we can learn from the evolution of security in other technologies. If you look at the lessons from cloud, a lot of the […]
Read MoreUnlock Gen AI Value Faster by Making Security Your Ally
Let’s jump to the punchline – business leaders and AI developers are in the unique position to prove they have considered meaningful security in their generative AI powered applications before security teams have fully defined the technical controls. How? By strategically focusing security considerations on tangible risks to the application use cases and their outcomes. […]
Read MoreTop 3 lessons generative AI security can learn from the cloud
For anyone who’s been in the industry for a while, we know that IT is cyclical. The technology changes, but the patterns remain the same. During the early cloud days, I heard from former COBOL and Unix programmers about the progression from renting time on early mainframes to personal computers, and back to running on […]
Read MoreRSAC 2025 – Wait, there’s more to security than gen AI?
Although originally not part of the plan (there’s a plan?), I was able to attend RSAC 2025 and see a couple of talks and hit the expo floor. I have to be honest; it was nice to see something, anything, not directly pushing generative AI hype (*cough* Google Next *cough*). Now don’t get me wrong, […]
Read MoreDeeper dive – Gen AI In Security: Gen AI powered threats
In our previous discussions, we delved into the platform-level risks, systemic-level risks, and the empowerment of security through generative AI. Now, let’s explore the darker side of this powerful technology: generative AI-powered threats. This topic is crucial as it highlights the potential misuse of generative AI in creating sophisticated and automated cyber-attacks. We’ll cover four […]
Read More